Usually to get apt you need to launch Cydia. If you only have an ssh connection in and would like apt you can go to http://apt.saurik.com/debs/ and grab berkeleydb_4.6.21-5_iphoneos-arm.deb and apt7_0.7.25.3-8_iphoneos-arm.deb. Scp them over and run dpkg -i apt7_0.7.25.3-8_iphoneos-arm.deb then dpkg -i berkeleydb_4.6.21-5_iphoneos-arm.deb. There you go. You can apt-get all of the things now.
Posts
- Tue 01 December 2015
Uninstall all installed windows KB patches in one line of batch
Thu 05 November 2015Category: Old Posts
I was trying to unpatch something to make it vulnerable and I was getting impatient trying to uninstall the correct patch so I got creative and came up with a one liner to uninstall all of them at once. Or at least all of the ones with working uninstallers and don't have other dependencies... The uninstallers are all called spuninst.exe and are somewhere in \\WINDOWS (under a bunch of sub folders that start with $NtUninstall) so I give you the following command:
for /F %a in ('dir /B /S /A \\WINDOWS ^\| findstr spuninst.exe ^\| findstr NtUninstall') do @(echo %a && %a /quiet /norestart)Keep running this until it does not print anything and then all of the patches will be gone on reboot. Happy unpatching
... bonus
for /L %b in (0,0,1) do @for /F %a in ('dir /B /S /A \\WINDOWS ^\| findstr spuninst.exe ^\| findstr NtUninstall') do @(echo %a && %a /quiet /norestart)Just keep running that until the screen is blank
Cobalt Strike 2.4 on Kali 2.0
Wed 21 October 2015Category: Old Posts
Cobalt Strike 3.0 came out lacking metasploit integration. Also, Cobalt Strike 2.4 (grab that here if you need it) doesn't work with the version of Metasploit that is built into Kali 2.0. That's okay, because you can still compile the metasploit framework to work with Cobalt Strike 2.4.
curl -sSL https://get.rvm.io \| bash -s stable source /usr/local/rvm/scripts/rvm apt-get install libpq-dev libpcap-dev service postgresql start msfconsole exit (this was to make sure the msf database was created) rvm install 1.9.3 cd /usr/share git clone https://github.com/rapid7/metasploit-framework cs-msf cd cs-msf git checkout dc48987 rvm use 1.9.3 bundle install for i in msf*;do update-alternatives --install /usr/bin/$i $i $PWD/$i 1;done cd ../metasploit-framework for i in msf*;do update-alternatives --install /usr/bin/$i $i $PWD/$i 2;done rm -rf $(dirname $(which msfconsole))/msf* update-alternatives --config msfrpcd < <(echo 1) cp /usr/share/metasploit-framework/config/database.yml /usr/share/cs-msf/config export MSF_DATABASE_CONFIG=/usr/share/cs-msf/config/database.ymlThen, edit the database.yml file @ /usr/share/cs-msf/config/database.yml:
- Delete the &pgsql after development
- Delete all profiles after development (after first line with nothing on it)
- Change development to production (1st line)
- Save the file
You should now be able to run cobalt strike 2.4 just fine.
To switch back just open a new terminal OR:
update-alternatives --config msfrpcd < <(echo 0) rvm use systemAnd the next time you want to use 2.4 (put this in a script):
\#!/bin/bash source /usr/local/rvm/scripts/rvm rvm use 1.9.3 update-alternatives --config msfrpcd < <(echo 1) export MSF_DATABASE_CONFIG=/usr/share/cs-msf/config/database.yml ./cobaltstrike &>/dev/null &disown read -p "Press enter once the RPC server has started up..." i update-alternatives --config msfrpcd < <(echo 0)I'm pretty sure there is a more elegant way to do this rather than using update-alternatives... but this works for now. As a side note... tracking down the exact revision where ruby 2.1 became a dependency was terrible. Yes, this is the absolute LAST commit you can get and compile without ruby 2.1. I might update this with a solution for later versions of metasploit before the MsgPack library update (which breaks cobaltstrike much more than I'm willing to fix!).
WMCSC Red vs. Blue Competition 2015
Wed 29 July 2015Category: Old Posts
Today I had the pleasure of participating in the West Michigan CyberSecurity Consortium's (WMCSC's) annual red vs. blue competition. In April I received an email from one of my professors about red teaming for this event and was interested because I like red teaming. I thought the experience would be worth the money I had made at my internship, so I decided to come out here to play. I was certainly right about it being worth it; I have done a bit of red teaming before, but this was the first time I was doing something without any knowledge of the infrastructure. The team that was gathered was mostly centered in Michigan, with a few people from other areas like myself. We started collaborating in mid July so that we could form a game plan. There were 11 people total on our red team lead my Mr. Matt Carpenter of Grimm. We spent a week or so talking about strategies and tools and then were given access one week before the actual event to try and breach systems and put backdoors in place. This infrastructure was broken up into a few different parts: the school, the power plant, Alphaville, (one other one I can't remember right now), and our target Zenda. Zenda was supposedly a research company we were supposed to hack as the Kneebonian Mafia. The infrastructure for the competition was put together by Merit, a company that was developing networking technologies back when ARPANET was starting to be more heavily used and other networks were popping up. The company now (among other things) runs the Michigan Cyber Range, which was the infrastructure we were playing on.
To gain access to the environment we had to log log onto Windows 7 machines via the VMWare Horizon View client, which connected to the Kali VMs via a remote service called NoMachine. Getting in was actually surprisingly easy, but I locked myself out a few times with a couple of dumb mistakes (I'll explain this in a second). The one disappointing aspect of this competition was that there was no internet within the environment, so we couldn't just go out and get tools and things without a bit of hassle. We ended up being able to upload packages to a web interface and access them from Kali, but this wasn't fully set up until Saturday or Sunday. We gained access to Kali on Thursday, but I didn't really end up doing much until I was able to get my toolset onto the box. They did not give us any IP address information, so I just tried scanning and poking at everything and eventually I ended up locking myself out twice, like I mentioned above. This is how I found out that I do stupid things when I'm not given targets!
When I scanned and saw the exposed outside (local) network I was a bit disappointed: it was Windows XP, Server 2003, and a lot of Linux 2.X. I thought that was it; we were going to own everything and make blue team cry, and be done in 20 minutes... but I was so wrong. Not long after scans had finished I quickly gained access to five or six Windows XP/2003 machines on that outside local network which was known as Alphaville (the 10.0.3.0/24 network). Our Kali boxes were also on this network. This was Monday, so I spent the day planting myself deep into these boxes with Cobalt Strike's beacons and other shenanigans I like to do to maintain access. One of the boxes was a Server 2003 domain controller for the school network (192.168.40.0/24), which had many hosts underneath it. Unfortunately I was having trouble getting to them, so I moved on and attempted to crack passwords for a bit. I ended up importing ophcrack's XP free small tables into the environment and trying to use those. Since Cobalt Strike and metasploit were already hogging most of my RAM I ended up using OCR to get the hashes on my local box and cracked them using the XP special tables. Through credential re-use I gained access to the Linux machine that the library website was hosted on and planted backdoors on that.
...
Check out the full post for more details!PoliCTF 2015 – John Pastry Shop – Pwnable 100 (aka how to make a pwndcake)
Sun 12 July 2015Category: Old Posts
This challenge was a pain in the ass, but it was still fun. It's funny that I really don't like java but I ended up solving the two java-based challenges in this CTF. Bleh. So this challenge had a set of files and a server to connect to. The files were Cake.java, Decode.java, and ShamanoCakeContainerEncoded.jar. The server was pastry.polictf.it 80. The description was
Among his hobbies, John likes baking cakes to eat during the warm afternoons in Milan. He is damn good at this such that, a couple of months ago, he decided to open a pastry shop on his own. The shop was an immediate success and John needed to bake just so many cakes that he decided to outsource the production of his famous NewYorkCheeseCake to another external and trusted pastry shop, the Shamano's (see shamanoPastryShop.pem). John provided Shamano's with the original basic recipe of his Cake (see Cake.java) and, after his customization, Shamano returns to John a cake container holding the NewYorkCheeseCake (see ShamanoCakeContainerEncoded.jar). Notice that Shamano has to follow John's directions carefully and that is why he always have to encode properly his cake containers so that John can verify all of them accordingly to a fixed decoding process (see extract of source code in Decode.java). John always tries his best for verifying the quality and genuineness of the incoming NewYorkCheeseCake but, you know, to busy people, like he is, it may sometimes happen to forget to check something.
So there is a Cake, a NewYorkCheeseCake, and a Decoder, that must be the three files. First, I wanted to see what the server would do upon sending it the ShamanoCakeContainerEncoded.jar file.
nc pastry.polictf.it 80 < ShamanoCakeContainerEncoded.jar Welcome to John's Pastry Shop! In John's opinion this cake container seems a trusted one from Shamano's Pastry Shop. And it also contains a valid NewYorkCheeseCake. This seems a tasty cake! Here are its ingredients: * Cream Cheese * Biscuits * Sugar * Isinglass Thanks for visiting John's Pastry Shop!Since it said something about encoding I wanted to make sure it was a jarfile.
file ShamanoCakeContainerEncoded.jar ShamanoCakeContainerEncoded.jar: dataAlright so it's encoded like it says, the file command should say it is a zip file since jars are just zips. Good thing there is a Decoder! ... well, most of a decoder: ...
Check out the full post for more details!PoliCTF 2015 - Crack me if you can - Reversing 100
Sun 12 July 2015Category: Old Posts
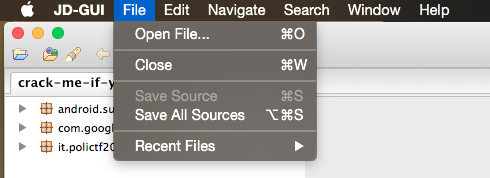
I untarred the challenge and in the folder: crack-me-if-you-can.apk. Awesome, I love reversing Android apps. I did what I always do when I get an apk: decompress and decompile it.
~/Dev/dex2jar/d2j-dex2jar.sh crack-me-if-you-can.apk apktool d crack-me-if-you-can.apkApktool complained about some of the resources since I don't have a framework-res.apk handy, but that's alright, I didn't need it to fully decompress anyway. Next, I loaded the jar file into JD-GUI and saved all of the sources from it as shown below.
 Then I unzipped and inspected the LoginActivity.java source file to see what the program was doing.
Then I unzipped and inspected the LoginActivity.java source file to see what the program was doing.mkdir sources && unzip sources.zip -d $\_ vim sources/it/polictf2015/LoginActivity.javaWhen reversing an android app I always start at the first activity and look at the OnCreate function.
protected void onCreate(Bundle paramBundle) { super.onCreate(paramBundle); setContentView(2130968599); if ((a(getApplicationContext(), 2)) \|\| (a(getApplicationContext(), "flagging{It_cannot_be_easier_than_this}")) \|\| (a(getApplicationContext(), false)) \|\| (a(getApplicationContext(), 2.78D))) Toast.makeText(getApplicationContext(), getString(2131492925), 1).show(); while (true) { this.a = ((EditText)findViewById(2131361877)); ((Button)findViewById(2131361878)).setOnClickListener(new a(this)); this.b = findViewById(2131361875); return; Toast.makeText(getApplicationContext(), getString(2131492922), 1).show(); } }...
Check out the full post for more details!PoliCTF 2015 - Hanoi-as-a-Service - Pwnable 50
Sun 12 July 2015Category: Old Posts
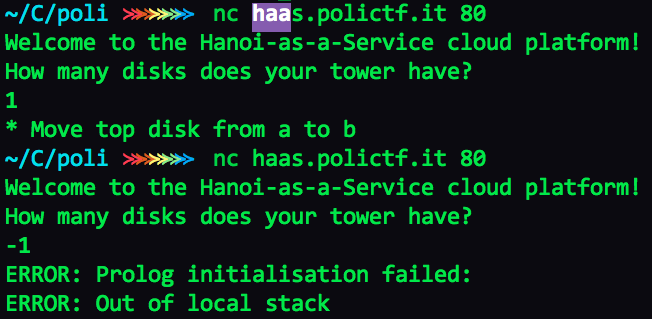
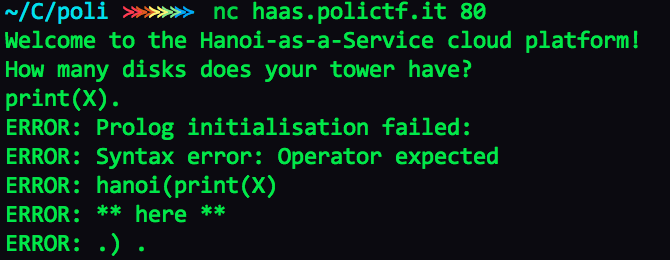
This challenge gave nothing but a URL: haas.polictf.it 80. For some reason the organizers decided to run a lot of their services on port 80. Netcatting in reveals a simple hanoi solver. Usually when given a service like this with no binary I start inputting values to see what information I can get or if I can cause any errors/crashes. I try a positive, then a negative number.
The program had an error, and it printed out for us. What is prolog?
Prolog is a general purpose logic programming language associated with artificial intelligence and computational linguistics. -Wikipedia
With a little bit of Googling around I tried some syntax:
It looks like it is taking our input and putting it directly between the two parentheses of the hanoi function. This is textbook command injection. To test, I decided to print something simple. ...
Check out the full post for more details!Some Metasploit Annoyances
Fri 27 March 2015Category: Old Posts
I don't know how I broke metasploit, but I did. It reported an incorrect password for the msf3 postgres user. Here's how I fixed it after some digging.
su - postgres psql postgres=# alter user msf3 with encrypted password 'mypasswordhere'; postgres=# \q vim /opt/metasploit/apps/pro/ui/config/database.ymlReplace database password with whatever password you just set and enjoy msfconsole and related tools again.
Sort of ROP
Tue 11 November 2014Category: Old Posts
I've been running through some exploit challenges recently to try and develop my skills a bit more. I was working on the exploit-exercises.com Protostar VM on some stack challenges for a bit today and ended up doing some Return Oriented Programming (ROP) to solve stack6 and stack7. It was interesting to work on so I thought that I would share here. I know it isn't 100% ROP (I use shellcode in the end) but that's alright, it got around the protections that these two challenges had in place.
Basically the gist of these two is that you can overflow a buffer of size 64 to get code execution. In these examples, however, there are some restrictions. In stack6 if you try and overwrite the return address with anything that begins with 0xbf (anything on the stack or in environmental vars), then it will exit and not run the shellcode you want it to. Unfortunate, but a nice challenge. Stack7 is similar but you cannot make the return address anything that starts with 0xb at all so it is a bit more restrictive. I was actually able to solve both at the same time with ROP. ...
Check out the full post for more details!Anti-Debugging
Mon 10 November 2014Category: Old Posts
I know anti-debugging and anti-reversing methods can be beaten fairly easily, but I played around with some today and thought it was worth sharing. My goal at the beginning was to be able to detect if a software breakpoint had been set (0xCC or 0xCD in memory). With a bit of searching around and figuring out different things I came up with the following code:
#include <unistd.h> #include <sys/types.h> #include <stdio.h> #include <stdlib.h> #include <signal.h> extern char __executable_start; extern char __etext; void check_bp(){ //Check debugger breakpoints (software) unsigned char bp1 = 0xCB; //We need to define the interrupt unsigned char bp2 = 0xCB; //codes without actually including them bp1++; bp2++; bp2++; //Point to the beginning of the .text section and then figure out the size unsigned char* ch = (unsigned char *)(unsigned long)&__executable_start; size_t size = (unsigned long)&__etext - (unsigned long)&__executable_start; //Scan through memory (.text) to find breakpoints :) for (size_t i = 0; i != size; i++){ if (ch[i] == bp1 || ch[i] == bp2){ printf("Breakpoint detected. @0x%lx: 0x%x\nAborting.\n", (unsigned long)&ch[i], ch[i]); raise(SIGSEGV); } } } int main(){ check_bp(); //do main stuff return 0; }The external symbol __executable_start denotes where the text section starts in Linux. The external symbol __etext denotes the end of the text section in Linux. Basically this code finds where the text section starts and the size of the text section then scans through it to look for 0xCC or 0xCD. If it finds a breakpoint then the address and hex code of the breakpoint are printed to the screen and a segfault is raised. This can easily be bypassed by skipping over the check_bp function in GDB, but it is still a neat proof of concept.
Other things that can help prevent debugging/reversing are checking LD_PRELOAD, checking ptrace, and obfuscating the code. The first two can be beaten by the same trick that the breakpoint finder can, but obfuscation is not as easily defeated because it just makes the code really hard to reverse. Perhaps a combination of all four things can make a safer program, or perhaps a kernel module that prohibits tracing/breakpoints from any userland program. Just thoughts.