This year I had the honor of competing on the Collegiate Cyber Defense Competition (CCDC) team for RIT. For those of you unfamiliar with the CCDC it is the largest collegiate cyber security competition in the entire country. Over 180 schools competed in qualifying competitions, 10 from each of the 10 regions competed and the winner from each region had the chance to compete in the National CCDC for the Alamo Cup. The competition consists of three main teams: blue, red, and white. The blue teams are teams of eight students from a school that try to secure and defend systems they are given during the competition. The systems they are given have critical services to maintain such as email or DNS and also are bullet ridden with security flaws. At the same time they are also responsible for injects, or business tasks such as set up a VPN or central logging. The red team is a group of security professionals that try to hack into the blue teams' systems and disrupt their services. Blue teams are responsible for detecting and reporting red team activity in the form of incident response reports. The white team is the team that sets up the competition, designs the systems that are used in the competition, and monitor teams as they defend their networks and complete injects. Qualifying events are usually around 8 hours long, regionals are usually two or three days, and finally nationals consists of two days.
For the past couple of years RIT has won the North East Collegiate Cyber Defense Competition (NECCDC) and gone onto nationals. This year was no exception. I would go into more detail about that but this post is mainly focussed on nationals. Last year was the same, except the team won the national championship, so the team this year had quite a name to live up to.
Over the past few months I have gotten to know each and every one of my team members. They are honestly some of the smartest and most driven people I have ever met. We practiced and competed for months before the Raytheon National Collegiate Cyber Defense Competition (RNCCDC) of this year in San Antonio, Texas.
Our time practicing involved studying multiple OSs, securing them, learning to run services on them, detecting and stopping attacks, and preparing for the worst. Having heard all about the competition from members of the team that were there last year I was both nervous and excited.
We had no idea what we were in for...
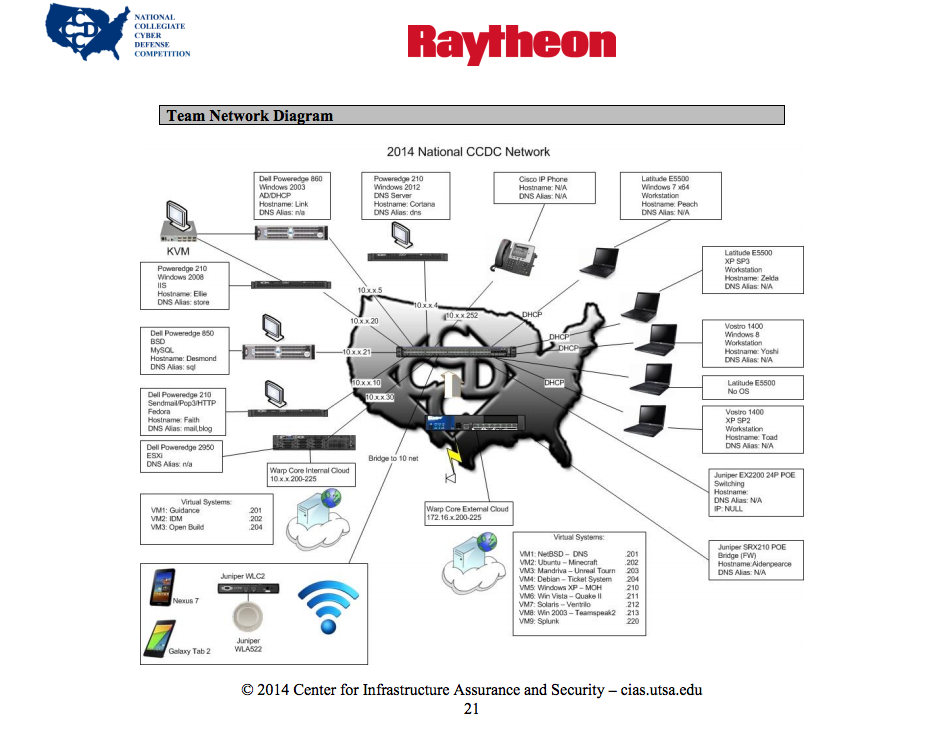
Our flight to Texas was on a Thursday with the first day of competition being Friday, a second day on Saturday, and then sponsor talks and an awards lunch on Sunday. We had no idea what we were in for when we woke up on Thursday. Last year the director of the competition send out the team packet on the Tuesday before with details about the infrastructure we would be running as well as services that were scored. This year we got it on that Thursday...
They were holding us responsible for twenty two systems (excluding networking devices) that included fourteen scored services: web shop , web ticketing system, web blog, cloud DNS, internal DNS, mail (POP3, SMTP), SSH, Minecraft, Unreal Tournament, Medal of Honor, Quake II, Ventrilo, and Teamspeak. We were running a gaming company called Warp Core Gaming. This was a big jump from the eight systems and seven scored services we had at regionals.
We knew we were going to get a large amount of systems but we thought there would be services that we knew how to manage completely. The challenge this year was to manage the games and chat servers in the cloud.
Despite getting second place in the main competition Bryan and I ended up teaming up with a couple of red teamers (Mubix and Egypt) to win the king-of-the-hill style competition that took place after day two called Panoply. We ended up taking first in that thanks to Bryan's scripts that he wrote for the RC3 competition.
RNCCDC was one of the best experiences of my life so far. I got to compete with and against the best in the industry, learned so many things to help me prepare for next year, and most importantly I got to know a fantastic group of guys I got to call my team. We were so wiped out after the two days and a total of about 18 hours of competition (plus panopoly) that some of us just fell asleep during some of the sponsor presentations (like the one about Walmart's hyperextended internal APT malcode darknet honeypot in the cloud).
As always a huge thanks to my team, everyone who supported me through this, the sponsors, the white team, CCDC staff, and anyone else I missed. Everyone put a lot of work in to make this all happen and give college students like me the opportunity to learn so much about cybersecurity from some of the best in the business. See you next year CCDC!